You focus on designing, building and managing our top shopping centers, schools, stadiums and skyscrapers. We'll manage every aspect of your I.T.
DESKTOP SUPPORT
Our team of help desk technicians and engineers can support all of your users' work devices, from laptops and desktops to smartphones to tablets.
APPLICATION SUPPORT
As the go-to IT firm for the AEC industry, we know your key applications, such as Newforma, Revit and AutoCAD.
I.T. SECURITY
We ensure you have the right gear, software and monitoring in place to both prevent and cope with a cyber attack.
INFRASTRUCTURE
We can assist your team in a new server, storage or networking refresh project and even support your entire infrastructure.
our AEC
PARTNERSHIPS

WE KNOW THE
AEC SPACE
LARGE FILE SIZES
Whether you are working with NewForma, one of the AutoDesk products, or a combination of all of the above, you work with some big files in this industry. Storage capacity and room for growth is always a priority.
SECURITY CONCERNS
You need a balanced security solution that not only protects your business data, but doesn't restrict your employees from working freely and efficiently from wherever they are.
LIMITED I.T. RESOURCES
Many people in the AEC industry are faced with limited I.T. resources, whether you have a small I.T. team or you've handed over the technology responsibilities to the most tech-savvy employee. It always feels like it's never enough.

our EXECUTIVE
LEADERSHIP TEAM
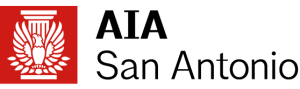
READ OUR
DELL CASE STUDY
Learn how Consuro helped Hahnfeld, Hoffer, Stanford Architects recapture billable time with infrastructure upgrades that dramatically improved Revit performance.
CHECK OUT
Our SERVICES

We specialize in the desktop and infrastructure management of environments for Architecture, Engineering and Construction firms. Whether you have a current IT staff internally and are looking to add additional technology management resources, or if you are needing to outsource 100% of your I.T. support, we have a plan for you.

You have a growing list of projects you need to complete, so let our team of certified engineers help. Whether you are lacking the time, resources or expertise, we can help you get there. Our projects center around application performance, servers, storage, networking, virtualization and private cloud, security, cloud services, email, backup & disaster recovery, wireless implementations, workflow optimization, and monitoring.
WE PARTNER WITH THE BEST





Contact Us
Whether you’re ready to scope out a project you’ve had on your list for months or if you are looking to fully outsource your I.T. and would like to start the conversation, let’s talk.
Phone: (877) 877-9876
Locations:
801 Cherry Street, Suite LLG50 Fort Worth, Texas 76102 4940 Broadway, Suite 122 San Antonio, Texas 78209 342 W Highland Blvd San Angelo, Texas 76903





